'Threat intelligence' technology can fight big box data breaches
Payments Source
DECEMBER 28, 2016
Data breaches have been proliferating over the past couple of years, but there's new technology out of the 'bot' and analytics worlds that can help.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Payments Source
DECEMBER 28, 2016
Data breaches have been proliferating over the past couple of years, but there's new technology out of the 'bot' and analytics worlds that can help.

PYMNTS
MARCH 25, 2020
The March edition of the Digital Fraud Tracker® explores recent developments, including the use of AI and ML to fight application fraud, the importance of separating good bots from bad bots, and the potential impact of the new coronavirus on the cybersecurity industry. Axos Bank on How to Separate the Good Bots From the Bad.

PYMNTS
OCTOBER 1, 2019
Another day, another data breach – at least it seems that way sometimes. In an interview with PYMNTS , Chipotle CTO Curt Garner explained how account takeovers primarily occur through automated bot attacks that have an identifiable signature. The latest involves DoorDash , and reportedly impacted around 4.9

PYMNTS
JANUARY 13, 2020
For example, firms are banned from using bots in a way that allows them to buy thousands of tickets for events and then resell them for highly marked-up prices. In an example of fines tied to data breaches and compromises, the Information Commissioner’s Office (ICO) is fining Dixons Carphone £500,000 (about $650,000).

Fintech News
MARCH 20, 2024
This tool is designed to help businesses tackle fraud rings, account takeovers, chargeback fraud, and bot attacks. Fraud networks, engaging in activities like multi-accounting, money laundering, and personal data breaches, target digital platforms such as cryptocurrency exchanges, fintech applications, dating services, and online casinos.

PYMNTS
JANUARY 27, 2021
Banks have reported myriad fraud threats over the past year, including various forms of identity fraud and bot activity, and are working overtime to develop countermeasures. Bot activity is the third major threat banks faced in 2020. utilize unique passwords for each of their accounts, for example.

PYMNTS
AUGUST 19, 2019
Here are some examples of restaurants and retailers that have bounced back from mobile data breaches and what they are doing to ensure security. Chipotle is on the route to recovery after suffering setbacks due to food safety concerns, falling sales – oh, and an April data breach. Chipotle .

PYMNTS
SEPTEMBER 17, 2020
Sharing economy businesses looking to keep their guests safe must deter data breaches that continually threaten organizations and can allow cybercriminals to steal usernames and passwords to access accounts. Other account takeover (ATO) schemes involve bots, which can conduct some 100 hits per second. More than 111 million U.S.

PYMNTS
JANUARY 28, 2020
Try wrapping your mind around the price tag of the average corporate data breach at $3.92 Combatting aggressive online fraudsters calls for asymmetrical strategies that confound mal-bots with superhuman processing power. In fact, phishing is the root cause of 90 percent of data breaches , including the giant commercial variety.

PYMNTS
JUNE 29, 2020
These credential abuse attacks come in a variety of forms, with some hackers choosing to overwhelm API defenses with simultaneous logins from a host of bots and others using more targeted techniques like phishing individual API developers and using their login credentials. There were 85.42 million were aimed at the financial industry.

PYMNTS
DECEMBER 21, 2020
As the Tracker notes, a recent data breach of a mobile order-ahead app leaked 2.8 Preventing these breaches is getting easier via platforming. Meanwhile, Kount’s Event-Based Bot Detection can stop malicious bots, allow good bots and quickly analyze, classify and adapt policies to new and questionable bots.”.

VISTA InfoSec
JULY 31, 2023
Segregation of Networks: This involves isolating the cardholder data environment (CDE) from the rest of the business’s network. Doing so can help reduce the scope of PCI DSS compliance and minimize the risk of data breaches. Avoid default settings for servers, software applications, and network devices.

PYMNTS
APRIL 24, 2018
Getting Their Hands on Data. There are a few ways in which fraudsters gain access to raw customer data. First, there are data breaches like the ones at Equifax, Target and other retailers. The vast majority of fraud attacks result from these data breaches. Separating the Wheat from the Chaff.

PYMNTS
JULY 13, 2020
A popular brute force method used to accomplish this is credential cracking , which involves fraudsters using bots to automatically plug potential usernames and passwords into login screens in the hopes of stumbling across the correct credentials.

FICO
OCTOBER 30, 2017
Due to the surge in data breaches, Social Security numbers, mailing addresses, passwords, health history, even the name of our first pet is all for sale on the Dark Web. Fraudsters use technology to implement bot net attacks that allow rapid exploitation of fraud control weaknesses before they are fixed.

PYMNTS
DECEMBER 20, 2019
Shape, for its part, protects the biggest airlines, retailers, government agencies and banks with complex fraud, abuse and bot defense. Shape, in particular, protects against credential stuffing attacks in which cybercriminals take over online accounts with stolen passwords from third-party data breaches.

Stax
MARCH 4, 2024
Taking precautions to implement security measures like firewalls and cybersecurity training helps to protect cardholder data and other sensitive information from cybercriminals. It’s also critical to ensure card information is protected from data breaches with secure encryption and cybersecurity standards in place.

Finovate
AUGUST 14, 2024
” Credential stuffing refers to a type of cyberattack in which a hacker uses credentials obtained through data breaches or purchased from the dark web in order to attempt to access another service. “This view arms companies with a proactive, first line of defense to detect sophisticated fraud rings and bot attacks.

PYMNTS
JANUARY 9, 2019
Stopping fraudsters can feel a bit like playing Whac-A-Mole for luxury retailers who want to protect customers and data, and no one wants to be the next retailer to experience a data breach or high-volume fraud attack. This is especially true as data breaches grow more common as eCommerce sales grow.

FICO
DECEMBER 13, 2017
We frequently talk about how PII data from data breaches is for sale on the dark web. I’m hoping to help level set for the non-techies: When we talk about brute force application fraud and bot-net attacks, what are we really talking about? In a similar vein, what is a “bot-net attack”?

PYMNTS
FEBRUARY 6, 2019
“Automation, mini-bots, machine learning and adaptive intelligence are becoming part of the finance team at lightning speed,” concluded analysis from Accenture, reports in Forbes said last year. But analysts warn that accountants and corporate finance professionals cannot simply go with the status quo.

PYMNTS
DECEMBER 13, 2019
According to one Mastercard study , about one-third of millennials and Gen Zers would let a bot plan their next trip in an automated fashion using data from their travel history. Platforms are doubling down on security in the wake of embarrassing data breaches and steady consumer fraud complaints, but it’s a fluid situation.

PYMNTS
JUNE 26, 2018
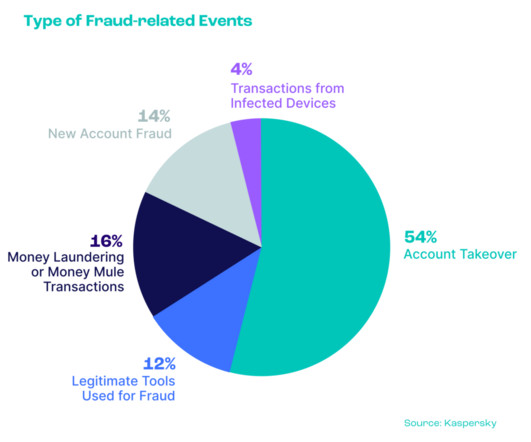
Perhaps, to no surprise, data breaches keep executives up at night — and the rest of us, too. One survey by Kaspersky Labs , across 2,000 consumers, found that 81 percent of Americans and 72 percent of Canadians are “stressed” about breaches. Furthermore, the company said that bots are being used to abuse stolen credentials.

PYMNTS
OCTOBER 23, 2017
If fraud attacks are the flu, then the Equifax data breach was a raging fever: a symptom (albeit a dramatic one) of a larger illness that will almost inevitably infect any organization that hasn’t had its shots. Bots are very efficient, and can be both a blessing and a curse – crack the code too efficiently, and it raises alarms.

PYMNTS
JULY 21, 2020
They might hack databases to obtain information like consumers’ emails and phone numbers or they might find such information already available on the dark web from previous data breaches. Payment app customers might confirm their identities by having their smartphones scan their fingerprints, for example.

PYMNTS
NOVEMBER 27, 2019
Customers and retailers are not the only ones being targeted, either: Fraudsters are also using automated bots to trick advertisers into paying money for false marketing impressions. Cybercriminals are thus increasingly turning to online platforms to perpetuate card-not-present (CNP) fraud.

FICO
JUNE 20, 2019
The ‘want it now’ culture of today’s consumer means that the technologies we all love to use for their convenience make it easier for fraudsters to do what they do, e.g., bots designed to test login credentials or to generate customer orders using stolen or synthetic identities. An increasing amount of data breaches across all industries.

PYMNTS
JANUARY 21, 2020
Advances in fraud decisioning have cybercrooks scrambling into the new arcana of synthetic identities and fiendish mass bot attacks, looking for any possible opening to exploit. The world of cybercrime is a veritable dunking in gloomy stats like that one, but the industry isn’t taking it lying down.

PYMNTS
JUNE 23, 2016
Carding may not be a new technique, but with the wealth of data floating around from larger data breaches and huge databases of compromised payment card data, it’s becoming a new favorite. It’s usually pretty organized,” Bush explained. Just to name a few.

FICO
JUNE 20, 2019
The ‘want it now’ culture of today’s consumer means that the technologies we all love to use for their convenience make it easier for fraudsters to do what they do, e.g., bots designed to test login credentials or to generate customer orders using stolen or synthetic identities. An increasing amount of data breaches across all industries.

FICO
JUNE 20, 2019
The ‘want it now’ culture of today’s consumer means that the technologies we all love to use for their convenience make it easier for fraudsters to do what they do, e.g., bots designed to test login credentials or to generate customer orders using stolen or synthetic identities. An increasing amount of data breaches across all industries.
Seon
JANUARY 29, 2024
Exploiting security vulnerabilities : This is where unpatched security holes are used to gain unauthorized access to a system.

PYMNTS
DECEMBER 3, 2016
A bunch of internet-connected devices gone bad and loaded up with bot armies that started attacking those beloved consumer sites. This was one of many data breaches this year that was eye-catching, as hackers managed to implant malware, spearfish their way into systems and make off with all kinds of consumer data.
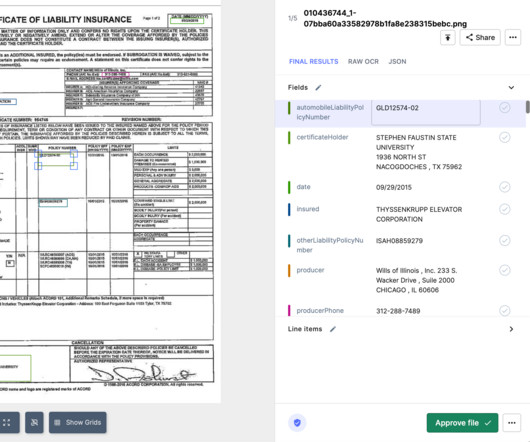
Nanonets
AUGUST 16, 2024
This enables automated data entry processes that lead to faster document review, lower processing time, and enhanced customer experience. RPA bots can handle tasks like data entry , verification of claim details, updating status in the claims management system, and even communication with customers.

PYMNTS
NOVEMBER 9, 2017
The executive said IntraNext isn’t fielding as many questions following the Equifax data breach as might be expected. Self-care, chat bots, artificial intelligence, and machine-to-machine learning is here to stay. Customers are not ready to make final decisions, and they certainly don’t want to make knee-jerk reactions.

PYMNTS
FEBRUARY 12, 2019
Now, different types of bots and scripts attack platforms, not one by one but thousands at a time,” he said. In the new Masterclass video, Lee summed up the evolution of fraud over the past decade or so, providing an observation that might lead to some anxious nights for merchants.

PYMNTS
DECEMBER 2, 2019
The offering allows Ticketmaster users to register for early announcements about shows they may be interested in attending and then make purchases through unique access codes provided by the company to ensure that fans, not bots, are given the first chances to buy tickets. The program’s goal is twofold, Karyo said.

PYMNTS
APRIL 14, 2017
Wonga had a whopper of a week as a data breach may have affected a quarter of a million U.K. The personal data tied therein may have been lifted, giving a black eye to the payday lender that is known for interest rates on loans that top 1,200 percent. But Bixby also has three big advantages.

PYMNTS
JULY 29, 2016
The data is out there — it’s good, it’s fresh and it’s being sold throughout the fraudster community, Bush pointed out. But the availability doesn’t just end with data breaches. Fraudsters are also able to rely on many tried-and-true techniques, such as spam emails, because they still work today.

CB Insights
JULY 20, 2017
Others companies in this subcategory include Zenedge , which offers a cloud-based, AI-driven Web Application Firewall (WAF), malicious bot detection, and DDoS cybersecurity solutions.

Seon
JUNE 21, 2023
Multi-use VCCs : With low-friction onboarding, fraudsters may use bots to try and generate cards en masse. As such, organizations need to be aware that VCCs are yet another digital temptation to attract online fraudsters, and that can lead to plenty of other layers of a data breach.
PYMNTS
NOVEMBER 11, 2016
Could Threat Intelligence Halt Data Breaches? The latest data from Imperva’s “ Combat Online Payment Card Attacks using Threat Intelligence ” report found that the total value of online credit card transactions at risk by 2020 will be $19 billion.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content